OS Basics : [Part 1] Lord of The CPU Rings
In this Blog post I am going to talk about some low level OS concepts (CPU modes, Protection Rings, etc). It is very unlikely that you will ever work on an operating system core. However, your software is always influenced by operating systems work and how a CPU executes your code .
Let's take things slowly. First we need to understand what is a CPU.
CPUs reside in almost all devices you own, whether it’s a smartwatch, a computer, or a thermostat. They are responsible for processing and executing instructions and act as the brains of your devices.
Why do we call a CPU a CPU?
At its core, a CPU takes instructions from a program or application and performs a calculation. This process breaks down into three key stages: Fetch, decode, and execute. A CPU fetches the instruction from RAM, decodes what the instruction actually means, and then executes the instruction using relevant parts of the CPU.
The executed instruction, can involve basic arithmetic, comparing numbers, jumping to another piece of code (performing a function), or moving data around in memory. Since everything in a computing device is represented by numbers (In Binary Format), you can think of the CPU as a calculator that runs incredibly fast.
CPUs are built by placing billions of microscopic transistors onto a single computer chip. Those transistors allow it to make the calculations it needs to run programs that are stored on your system’s memory. They’re effectively minute switches that switch on or off, thereby conveying the ones or zeros that translate into everything you do with the device, be it watching videos or writing an email.
CPU cores ?
Originally, CPUs had a single processing core. Today’s most modern CPU consists of multiple cores that allow it to perform multiple instructions at once, This is done by placing multiple CPUs in the the same silicon chip. Most CPUs sold today have two or four cores. Six cores are considered mainstream, while more expensive chips range from eight to a massive 64 cores that are usually used in servers.
Many processors also employ a technology called multithreading. Imagine a single physical CPU core that can perform two lines of execution (threads) at once, thereby appearing as two “logical” cores on the operating system end. These virtual cores aren’t as powerful as physical cores because they share the same resources, but overall, they can help improve the CPU’s multitasking performance when running compatible software.
What is an OS
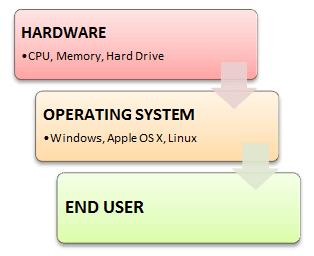
An Operating System (OS) is a software that acts as an interface between computer hardware components and the user. without it you basically have a very fast calculator that can do nothing on its own. For every program that you need to write you would have to implement all the level functionality yourself like (reading data stored on disks, producing sounds, drawing graphics on the screen, reading and writing files etc..) your program will also need to take into account every type of graphics card, sound card, hard disk, screen on the market because yes (every different brand has its own way of working).
An Operating System sits between your user program & the computer hardware. It abstracts away the hardware details from you so that most developers can focus only on what matters for them (the user software) and leave out all the low level hardware interactions to be done by the OS. for example and if you are writing python code that looks like that
with open("file.txt") as input_file:
print(input_file.read())
These two small lines have used a lot of functionality that was provided by OS which include:
- reading file "file.txt" from hard desk to memory
- printing file contents to stdout (standard output : Console)
- Closing file.txt
What is a Process
In computing, a process is the instance of a computer program that is being executed by one or many threads. It contains the program code and its activity. Depending on the operating system (OS), a process may be made up of multiple threads of execution that execute instructions concurrently.
While a computer program is a passive collection of instructions typically stored in a file on disk, a process is the execution of those instructions after being loaded from the disk into memory ( RAM) . Several processes may be associated with the same program; for example, opening up several instances of the same program often results in more than one process being executed.
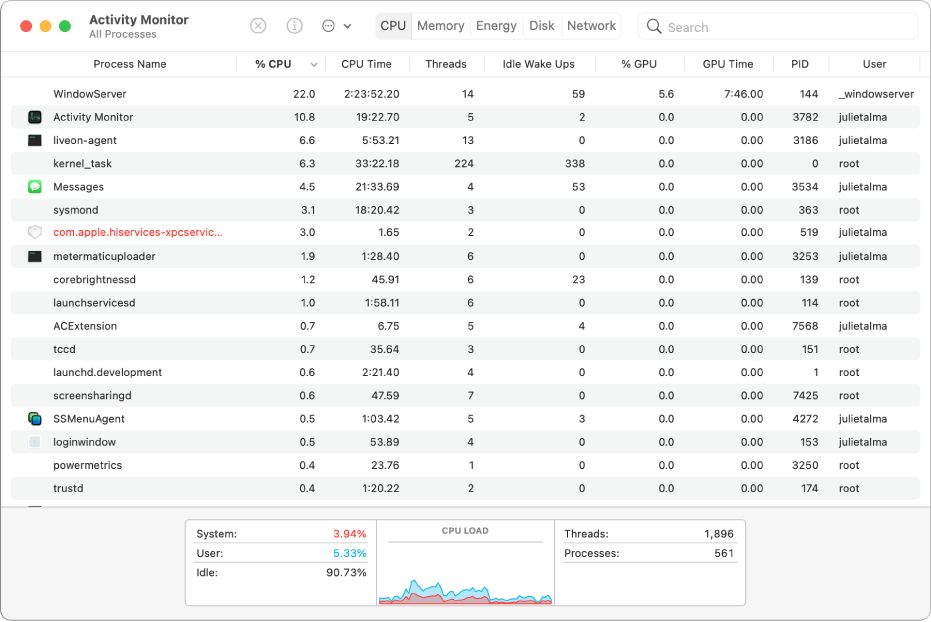
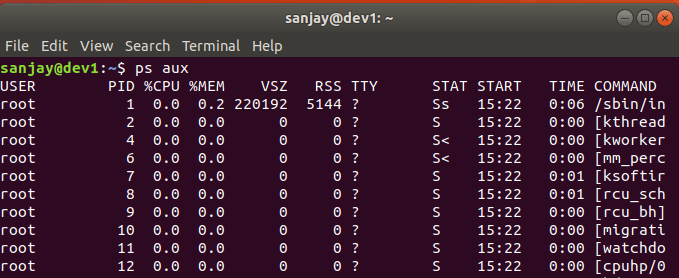
If you want to see the current processes running on your machine you can do the following
Mac OS
On a Mac machine can view the running processes on your machine by openning "Activity Monitor" from your spotlight search. Notice the process Id on one of the columns
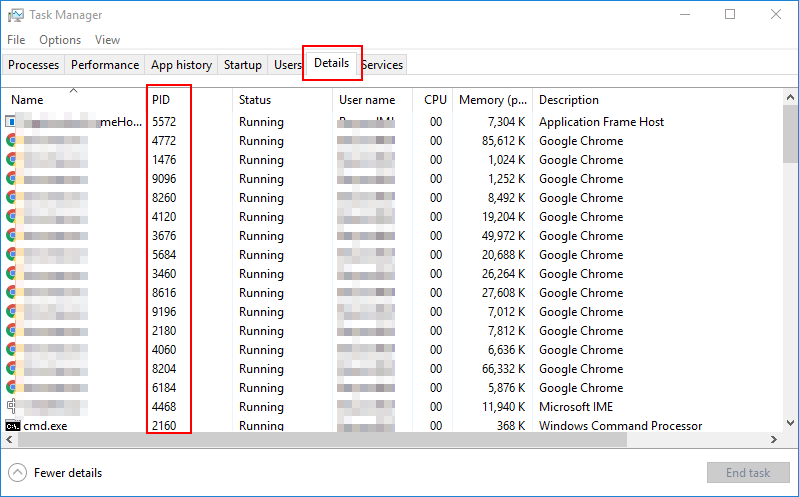
Windows
You can find a similar view on a windows machine by opening "Task Manager" on a Windows machine
Linux
On a linux machine it is as simple as invoking the following command on the terminal.
ps -l
What is OS Kernel ?
A Kernel is a computer program that is the heart and core of an Operating System. Since the Operating System has control over the system so, the Kernel also has control over everything in the system. Whenever a system starts, the Kernel is the first program that is loaded because the Kernel has to handle the rest of the thing of the system for the Operating System. The Kernel remains in the memory until the Operating System is shut-down.
The Kernel is responsible for low-level tasks such as disk management, memory management, task management, etc. It provides an interface between the user and the hardware components of the system. When a process makes a request to the Kernel, then it is called System Call.
Functions of a Kernel
In a nutshell the kernel is responsible of the following tasks:
- Access Computer resource: A Kernel can access various computer resources like the CPU, I/O devices and other resources. It acts as a bridge between the user and the resources of the system.
- Resource Management: It is the job of a Kernel to share the resources between various process in such a way that there is uniform access to the resources by every process and that there is no overlap.
- Memory Management: Every process needs some memory space to run. So, memory must be allocated and deallocated for its execution. All these memory management is done by a Kernel.
- Device Management: The peripheral devices connected in the system are used by the processes. So, the allocation and deallocation of these devices is managed by the Kernel.
What are CPU Modes ?
CPU modes (also called processor modes, CPU states, CPU privilege levels and other names) are operating modes for the central processing unit of some computer architectures that place restrictions on the type and scope of operations that can be performed by certain processes being run by the CPU. This design allows the operating system to run with more privileges than application software.
Ideally, only highly trusted kernel code is allowed to execute in the unrestricted mode; everything else (including non-supervisory portions of the operating system) runs in a restricted mode and must use a system call (via interrupt) to request the kernel perform on its behalf any operation that could damage or compromise the system, making it impossible for untrusted programs to alter or damage other programs (or the computing system itself).
In practice, however, system calls take time and can hurt the performance of a computing system, so it is not uncommon for system designers to allow some time-critical software (especially device drivers) to run with full kernel privileges.
Multiple modes can be implemented—allowing a hypervisor to run multiple operating system supervisors beneath it, which is the basic design of many virtual machine systems available today.
Protection rings
In computer science, hierarchical protection domains, often called protection rings, are mechanisms to protect data and functionality from faults (by improving fault tolerance) and unwanted malicious behavior.
Computer operating systems provide different levels of access to resources. A protection ring is one of two or more hierarchical levels or layers of privilege within the architecture of a computer system. This is generally hardware-enforced by some CPU architectures that provide different CPU modes at the hardware or microcode level.
Rings are arranged in a hierarchy from most privileged (most trusted, usually numbered zero) to least privileged (least trusted, usually with the highest ring number). On most operating systems, Ring 0 is the level with the most privileges and interacts most directly with the physical hardware such as the CPU and memory.
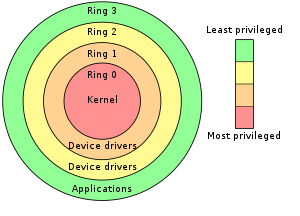
Privilege rings for the x86 available in protected mode
Many modern CPU architectures (including the popular Intel x86 architecture) include some form of ring protection, although the Windows NT operating system, like Unix, does not fully utilize this feature.
Ring protection can be combined with processor modes (master/kernel/privileged/supervisor mode versus slave/unprivileged/user mode) in some systems. Operating systems running on hardware supporting both may use both forms of protection or only one.
Effective use of ring architecture requires close cooperation between hardware and the operating system. The reason is Operating systems are designed to work on multiple hardware platforms may make only limited use of rings if they are not present on every supported platform. Often the security model is simplified to "kernel" and "user" even if hardware provides finer granularity through rings.
CPU Modes
Supervisor mode
In computer terms, supervisor mode is a hardware-mediated flag which can be changed by code running in system-level software. System-level tasks or threads will have this flag set while they are running, whereas userspace applications will not. This flag determines whether it would be possible to execute machine code operations such as modifying registers for various descriptor tables, or performing operations such as disabling interrupts. The idea of having two different modes to operate in comes from "with more control comes more responsibility" – a program in supervisor mode is trusted never to fail, since a failure may cause the whole computer system to crash.
Some examples from the PC world:
Linux, macOS and Windows are three operating systems that use supervisor/user mode. To perform specialized functions, user mode code must perform a system call into supervisor mode or even to the kernel space where trusted code of the operating system will perform the needed task and return the execution back to the userspace.
Hypervisor mode
Recent CPUs from Intel and AMD offer x86 virtualization instructions for a hypervisor to control Ring 0 hardware access. both Intel VT-x (codenamed "Vanderpool") and AMD-V (codenamed "Pacifica") create a new "Ring −1" so that a guest operating system can run Ring 0 operations natively without affecting other guests or the host OS.
To assist virtualization, VT-x and SVM insert a new privilege level beneath Ring 0. Both add nine new machine code instructions that only work at "Ring −1", intended to be used by the hypervisor.
What is Next ?
Next Time we will talk about different types of debuggers and how can we use them to debug applications running at different ring levels (how to debug kernel code for example)

![Information Security Series: [Part2] Principles of Privileges](/_next/image?url=https%3A%2F%2Fcdn.hashnode.com%2Fres%2Fhashnode%2Fimage%2Fupload%2Fv1647290198557%2FdaFz7fDND.png&w=3840&q=75)
![Information Security Series: [Part1] Principles of Security](/_next/image?url=https%3A%2F%2Fcdn.hashnode.com%2Fres%2Fhashnode%2Fimage%2Fupload%2Fv1647209120646%2FxVK4QYmwq.png&w=3840&q=75)